What Is DORA (Digital Operational Resilience Act)?
The Digital Operational Resilience Act, or DORA, is the European Parliament’s attempt to foster technological development, financial stability and consumer protection. After the financial crisis 2007-2008, regulations, such as Basel III, focused on the financial stability of financial institutions. In the face of an increasing number of cyber-attacks and other information and communications technology (ICT) breaches, digital resilience for the whole financial sector is gaining importance.
DORA was proposed in 2020 by the European Commission and the European Council Presidency and the European Parliament to help build a framework for financial institutions and their service providers. The draft version of DORA was adopted by the Council in November 2022. It is designed to consolidate and mitigate ICT risks in the financial sector and ensure all participants of the financial system are subject to a common set of standards. The legislation requires firms to ensure they can withstand all types of ICT-related disruptions and threats.
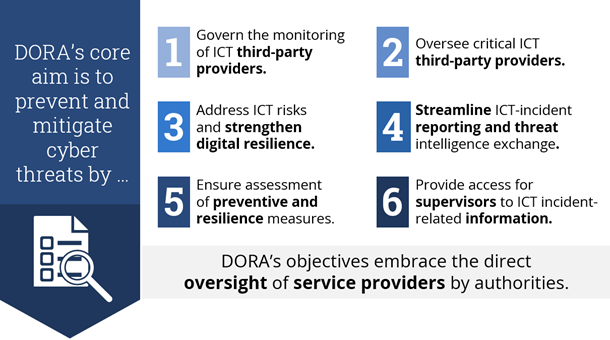
Figure 1: The Six Objectives of DORA
Broader Applicability of DORA Regulations in the Provider Ecosystem
In contrast to previous regulations, DORA focuses on a broad range of financial institutions as well as crypto-asset service providers, data reporting service providers and their ICT third-party service providers. Of course, all companies in scope will need to comply with the DORA requirements once it is in effect and ensure their auditability. This means they will need to be ready for an audit and have the internal capacity to respond quickly to audit requests.
An audit is a sport of its own. Don’t underestimate the resources needed to handle regulatory audits. Here’s what to know:
- Audits are typically announced four weeks in advance and can be ad hoc or repeated on a three-year cycle.
- Audits focus on the identification of risks and weaknesses and actual compliance gaps and are a combination of interviews, document reviews and on-site inspections.
- Evidence must typically be provided within 24-48 hours.
- An audit team usually consists of six to 10 full-time employees and will be executed over a time span of four to 10 weeks.
- Auditors' expectation is to have one single point of contact available full-time.
Complying with regulations is an ongoing journey. An actual audit is followed by regular progress updates and conversations with authorities about the findings and related mitigation actions. Authorities will return to run a follow-up audit, which will likely expand to include a new set of topics.
3 Key Steps to Prepare for DORA Compliance
Are you a financial institution? DORA will bring additional requirements to your existing compliance activities.
Though compliance with DORA will require adoption on every level of a financial institution, do not to be afraid. You most likely have already mastered the adoption of supervisory requirements. The maturity of the organization will determine how much adjustment is required to be compliant with DORA.
An adoption plan should include the following steps:
- Identify the potential downstream impact, but don’t lose yourself in the details immediately. Break it down and map the six DORA objectives to your
- Relevant policies and instructions
- Structures and procedures
- Retained organization
- Assess your environment to identify any gaps and additional requirements; evaluate the operational risk according to your operational risk procedures and risk appetite (within the norms of DORA)
- Plan a realistic two-year mitigation roadmap
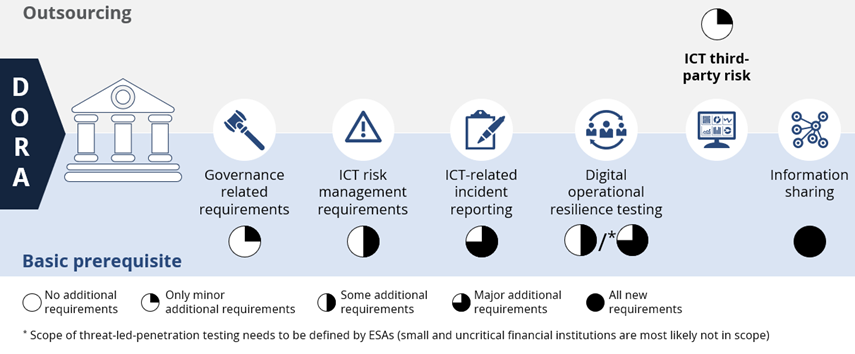
Figure 2: Financial institutions should focus on additional requirements regarding ICT-related incident and risk reporting
Are you a service provider? DORA’s objectives include the direct oversight of service providers. That’s a game changer given the growing enterprise dependence on third-party service providers for services such as cloud resources and data analytics. Both companies on the receiving end and the providing end of IT services and products will need to assess the impact in scope.
As a service provider, you should make some strategic decisions before you take DORA by the horns.
- Determine if you are in fact an ICT service provider for financial entities
- Decide if you are willing to pay the (extra) price to be part of the financial industry? Are you prepared for the consequences of constantly evolving regulatory requirements?
- If so, identify the potential impact, perform a gap analysis and define a distinct roadmap
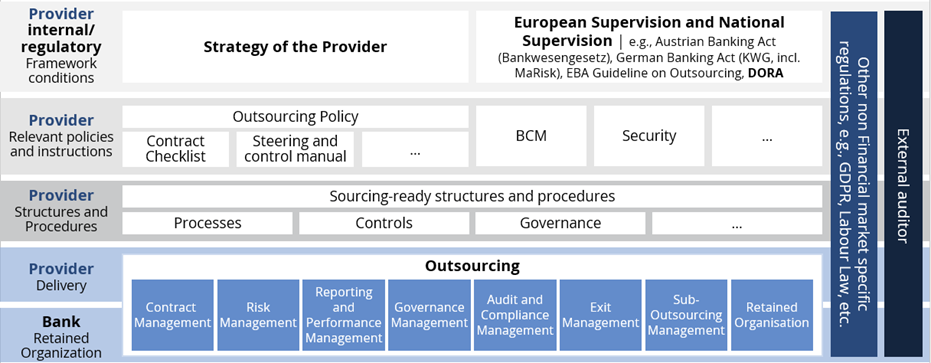
Figure 3: DORA will require adoption on every level within the organization
The Organizational and Technical Implementation of DORA
Compliance with DORA requirements is essential for staying in business. The penalty for non-compliance can be as high as the average daily worldwide turnover of the company until compliance is achieved. Therefore, we highly recommend you ensure compliance with the DORA requirements in a timely manner.
For third-party ICT service providers, early compliance provides a competitive advantage and an opportunity to increase market share. All institutions – either directly in scope or indirectly because of business relations with a company in scope – should review and, if necessary, renegotiate relevant contracts with regard to mandatory components.
ISG’s Banking Compliance & Management Framework helps you comply with DORA regulations with a compliance assessment that ensures you implement the right policies, guidelines and processes. This can be in the form of provider management (e.g., a review of the existing contracts in scope), audit preparation, interim management that performs tasks that require regulatory knowledge or training-on-the job. Contact us to find out how we can support you with DORA compliance.

Download ISG's introduction to DORA Compliance and Risk Management
