Secure access service edge (SASE) has moved from an emerging architecture to a strategic priority for enterprises facing hybrid work, cloud acceleration and rising cyber risk. SASE is not merely a security refresh. It is a broader business and operating-model transformation lever that enterprises need to approach pragmatically.
SASE delivers its strongest value when positioned as an enabler of simplification, cost rationalization and improved user experience, with security as a foundational – but not exclusive – driver. Organizations that approach SASE solely as a security project often fail to realize its full economic and operational benefits.
This paper gives decision-makers:
A concise explanation of SASE and its architectural foundations
A rationalized view of cloud, AI and hybrid work drivers
Key business value levers and cost considerations
Implementation risks and mitigation strategies
Strategic recommendations for enterprise adoption
What Is SASE and What Are Its Architectural Foundations?
SASE reflects the convergence of networking and security into a unified, cloud-delivered model. As enterprises adopt hybrid workforces, cloud-native applications and distributed infrastructure, traditional perimeter-based security and legacy wide-area network (WAN) architectures are no longer sufficient.
SASE is built on the principle of identity-driven access, where policies are enforced based on user, device, location and risk. This paradigm shift moves away from static, location-based security models to dynamic, context-aware enforcement. At its core, SASE combines several key components:
Software-defined wide-area networking (SD-WAN): optimizes and secures connectivity across distributed locations, ensuring high performance and reliability for cloud applications
Zero trust network access (ZTNA): enforces strict identity verification and access controls, ensuring that only authorized users and devices can access specific applications and data
Firewall as a service (FWaaS): provides cloud-based firewall capabilities, delivering advanced threat protection and consistent security policies across all locations
Secure web gateway (SWG): protects users from web-based threats by filtering malicious traffic and enforcing acceptable use policies
Cloud access security broker (CASB): ensures secure access to cloud services by monitoring and controlling data flow between users and cloud applications
These services are delivered via a cloud-native architecture, distributed across global points of presence (PoPs) to ensure low latency and high availability. This architecture also makes possible the single-pass inspection model that further enhances performance by enabling unified traffic analysis for threats, data loss prevention and access control in one streamlined process.
Key enterprise SASE use cases include remote workforce enablement, cloud migration, branch office security, IoT and edge computing security. AI-powered SASE enhances these use cases by enabling real-time threat detection, intelligent traffic routing and self-healing networks. User and entity behavior analytics (UEBA) further strengthens security by proactively identifying anomalies and mitigating risks. These capabilities support seamless connectivity, improved user experience and resilient operations in distributed environments.
Today, the SASE model should be viewed not as a technical upgrade, but as a foundational element of digital transformation, aligning with cloud adoption and decentralized operations. Near-term market evolution includes increased integration of AI-driven capabilities and continued SD-WAN evolution. Many enterprises will not move to full SASE in a single step: ISG notes that SSE accounts for roughly half to two-thirds of a complete SASE architecture, making it a practical intermediate stage for organizations that already have SD-WAN in place.
Please fill out this form to continue.
SASE Technology Drivers
Why are enterprises adopting SASE? There are six important reasons.
1. Cloud-Native Transformation:
SASE reflects the shift toward cloud-centric networking and security. As organizations adopt hybrid work, cloud-native applications and distributed infrastructure, perimeter-based security and legacy WAN models are increasingly insufficient.
Cloud migration with SASE enables secure connectivity for cloud applications while maintaining compliance and policy consistency.
2. Hybrid Work
Hybrid work is a primary driver of SASE adoption. Organizations require secure, reliable access for distributed users and branch locations. SASE enables a zero trust model by enforcing identity-based access controls, ensuring users only access approved applications and resources. SD-WAN configurations are increasingly tailored by site type, balancing performance and cost across enterprise locations.
3. IoT / Edge Computing
The expansion of internet of things (IoT) and edge computing increases the need for distributed security enforcement. SASE enforces policies across remote devices and edge environments in support of secure and resilient operations.
4. AI & Automation
AI is becoming a core enabler of modern SASE platforms. AI-driven capabilities include:
-
real-time threat detection
-
automated response and remediation
-
predictive analytics for network optimization
-
anomaly detection via behavioral analysis
Enterprises that can integrate SASE with AIOps will support self-healing networks, reduce operational overhead and improve user experience.
5. Cyber Threat Landscape
The evolving threat landscape is accelerating SASE adoption. Organizations across industries require integrated security platforms that combine threat prevention, analytics and automated enforcement. AI-enhanced detection and response capabilities help organizations address increasingly sophisticated and fast-moving cyber threats.
6. Compliance & Regulatory Pressure
Regulatory frameworks such as NIS2 and DORA are driving demand for centralized policy control and consistent data protection. Compliance requirements such as GDPR reinforce the need for strong encryption, access control and auditability.
SASE introduces centralized security policy management and unified controls, greatly simplifying audits and traceability, while natively integrating data protection mechanisms such as data loss prevention (DLP), CASB, SWG, and ZTNA within a single framework.
Data residency remains a significant challenge in the context of SASE. Inspecting traffic and data as they traverse various PoPs can complicate compliance, especially when regulations require data to stay within specific jurisdictions. This topic deserves special attention during SASE architecture design to ensure that centralization and automation do not compromise local data residency obligations. While the link between compliance and SASE is a true lever for innovation and differentiation for organizations, it also demands heightened vigilance around data handling and inspection.
SASE Market Dynamics
The SASE market is experiencing rapid growth, driven by the increasing demand for secure, agile and scalable connectivity solutions. According to industry reports, the global SASE market is projected to reach $17.92 billion by 2026, with a compound annual growth rate (CAGR) of 23.6%. Over 65% of organizations have adopted or plan to adopt SASE.
As adoption increases, the SASE vendor market is experiencing strong growth. Industry forecasts indicate continued expansion with strong CAGR driven by enterprise demand for integrated networking and security platforms. Vendors are enhancing their portfolios with integrated SD‑WAN capabilities, cloud‑delivered security and AI-driven analytics into unified offerings.
Enterprises that are looking for a SASE partner should know that convergence of networking and security reduces complexity, lowers total cost of ownership and improves scalability.
SD-WAN Strategic Maturity
SD-WAN is evolving from connectivity optimization to a foundational component of SASE architectures. SD-WAN is no longer a standalone solution. Its convergence with SASE architectures is reshaping enterprise connectivity. Enterprises are taking advantage of SD-WAN solutions that converge with security services and embed identity, conditional access and continuous trust verification.
The traditional fully managed SD-WAN model is increasingly complemented by co-managed and DIY approaches. These alternatives are driven by enterprises seeking greater control over transport layers, security domains and service orchestration. In Europe, co-managed and DIY SD-WAN models now hold a slightly larger market share than fully managed services. Providers are embedding identity services, conditional access and continuous trust verification directly into SD-WAN platforms.
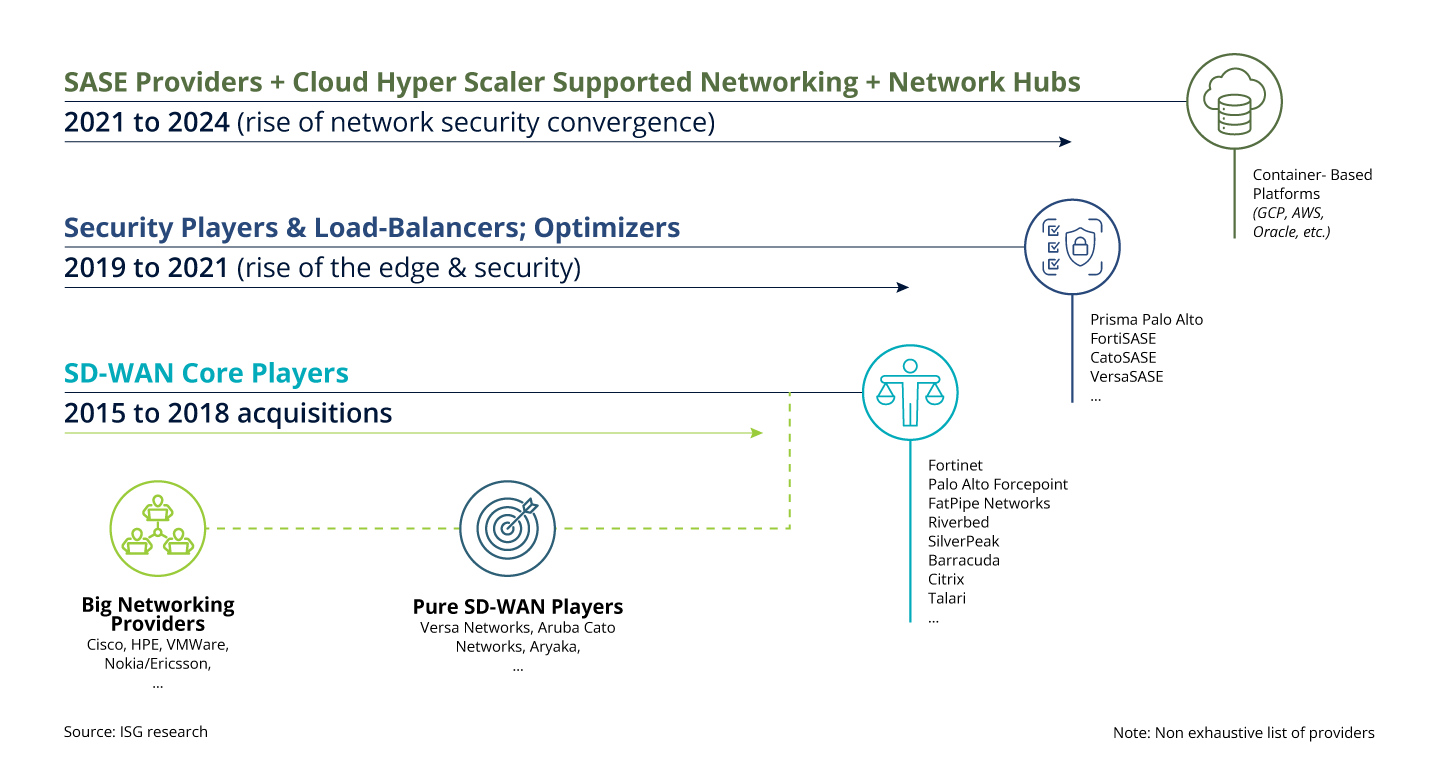
Figure 1: Evolution of the SASE Market
Despite inflationary pressures, SD-WAN pricing remains competitive due to vendor rivalry and automation-driven efficiencies. Enterprises are leveraging SD-WAN to reduce MPLS costs, improve application performance, and enhance network resilience.
Enterprises are increasingly tailoring SD-WAN configurations to site typologies. Critical sites, such as data centers and regional hubs, receive advanced service tiers with high availability and embedded security. Secondary sites, including retail branches or remote offices, are provisioned with standard or basic tiers, balancing cost and performance.
Tooling & Observability
Modern SASE environments rely heavily on integrated tooling and observability frameworks.
Tooling interfacing is crucial in modern IT environments, as it ensures seamless integration and communication between various systems and tools. API connectivity plays a vital role in this process, enabling the interaction between cyber tools and IT Service Management (ITSM) tools. This connectivity allows for the automation of workflows and real-time data exchange.
Additionally, a robust observability layer is essential for monitoring and analyzing system performance. Observability tools collect and analyze data from various sources, including logs, metrics and traces to provide a comprehensive view of the health and performance of applications and services. This data aggregation allows for the correlation of events and detection of anomalies across the entire infrastructure, from the user to the cloud. By leveraging machine learning and advanced analytics, observability tools can identify patterns and predict potential issues before they escalate.
Implementation Challenges and Mitigation
Though organizations may understand SASE is the direction of the future, implementation can pose challenges. For most organizations, these include legacy system integration, widening skills gaps, policy complexity and organizational silos that make communication and alignment difficult.
Successful deployment requires coordinated execution across networking, security and cloud teams. Enterprises need a structured and phased migration plan. Many ISG clients find that managed service partnerships are effective ways to address talent shortages. Adopting centralized management consoles and unified enforcement mechanisms can greatly simplify oversight, ensuring that policies remain consistent across diverse environments.
The integration of networking and security functions calls for enhanced collaboration and communication between previously distinct teams. Promoting cross-functional cooperation is essential for breaking down barriers and achieving cohesive, well-coordinated SASE operations.
Strategic Recommendations for Implementing SASE
SASE should be treated as a transformation initiative rather than a tooling upgrade. Enterprise leaders should follow these seven steps:
-
Define clear objectives aligned with business goals, such as enhancing security or enabling digital transformation.
-
Select modular, software-based platforms that support flexible integration and scalability.
-
Evaluate vendors based on PoP coverage, service consistency and AI capabilities, as well as exploring network-as-a-service synergy to optimize network and cloud invoicing.
-
Start with high-impact use cases to demonstrate value and build momentum.
-
Foster cross-functional collaboration and invest in continuous monitoring and optimization.
-
Evaluate the potential added value of an integrated observability layer to create a cohesive and resilient IT ecosystem that is proactive and adaptable.
-
Leverage AI-powered analytics and AIOps to enhance performance, security, and compliance.

Figure 2: Strategic Opportunities for SASE
SASE represents a structural shift in enterprise networking and security that enables unified, cloud-delivered operations. The future of SASE is poised for continued innovation and growth, fueled by emerging technologies such as 5G, edge computing and quantum-resistant encryption. In this environment, organizations must stay abreast of advancements and adapt their strategies to leverage new capabilities and counter evolving threats, ensuring robust security, seamless connectivity and resilient operations in an increasingly digital world.
Implementing SASE is inherently complex. It requires onboarding multiple regions, adapting to regulatory and technological specificities and integrating networking, cloud and security domains. Success hinges on selecting the right vendors and service providers. Evaluation must include their ability to handle regional compliance, API compatibility with existing systems, observability and proven experience in SASE deployments
SASE is no longer experimental; it is a strategic decision point for enterprise architecture. Before they get started, organizations should consider the following questions:
-
What are the actual costs of our current complexity and fragmentation?
-
What are our desired business outcomes over the next 24 months?
-
How ready are we for converged networking and security models?
Organizations that fail to modernize their security environment will risk increased complexity and security exposure. Those that adopt SASE will gain scalability, resilience and operational efficiency.
